Dark Web Monitoring – What is written about you on the Darknet!
In the depths of the internet lies a hidden world: the dark web. A place where the rules of the normal Internet do not apply and which harbors both opportunities and immense risks. But what is really behind this mysterious part of cyberspace? And how can you monitor the dark web to find out whether your personal data is being traded or sold there? Our Dark Web Monitoring article will tell you.
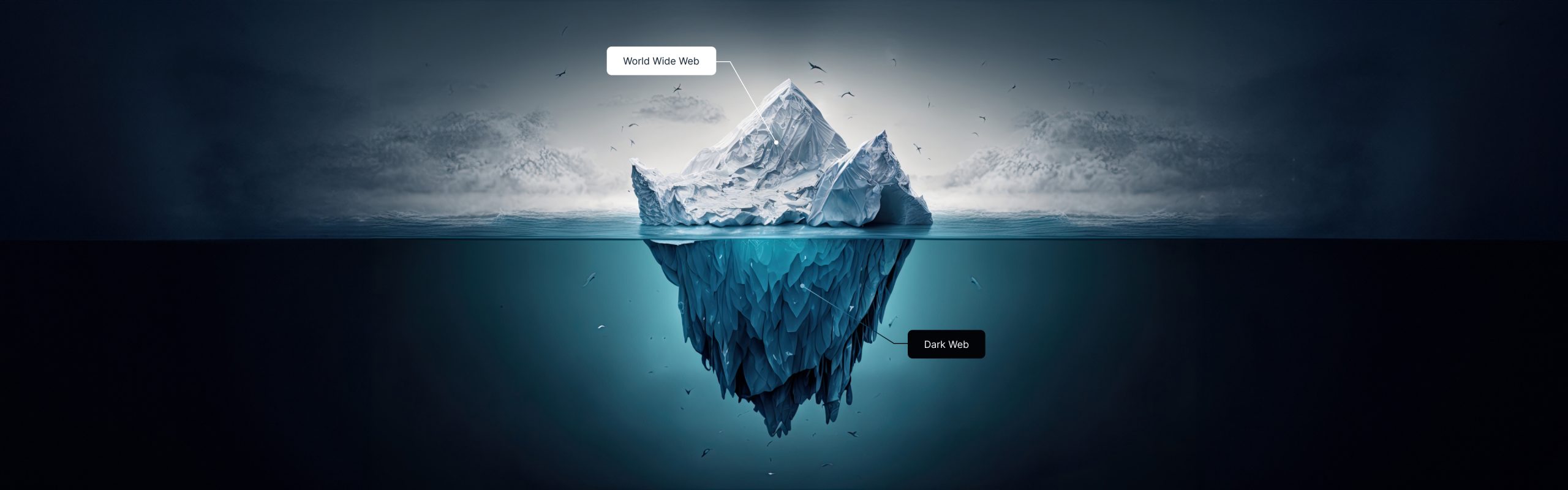
What is the dark web?
The dark web is an encrypted part of the Internet, accessible only through special software. Here, shielded from the usual search engines, you can often find bizarre, forbidden and criminal content that would be unthinkable on the normal Internet.
Differences between dark web, deep web and regular internet

-
Regular Internet and Deep Web
While the regular Internet is the publicly accessible part of the World Wide Web, the deep web comprises content that cannot be found using conventional search engines but can still be accessed without special software. -
Dark Web
The dark web is a small but distinctive area of the deep web. It is notorious for the anonymity it offers its users. The security and accessibility of this area are only possible with special tools, above all the Tor browser.
Risks and threats on the dark web
Cyber criminals use the dark web to remain undetected. Threats such as data leaks, contract killings, identity theft or sophisticated hacker attacks can be found here. These threats pose a significant risk to businesses and individuals, which underlines the need for dark web monitoring.
For example, e-mail addresses and passwords from company hacks are traded on the dark web. With this combination of email address and password, criminals can commit identity theft or log into online services such as Amazon, eBay or bank accounts, as many users often use the same combination of email and password for different online services.
For example, fraudsters commit fraud by ordering expensive products in an online store but changing the shipping address. Of course, they have previously changed the e-mail address of the account so that the person concerned is not notified. These and similar scams cause around 8 billion euros worth of damage every year – and the trend is rising.
What is dark web monitoring?

Dark web monitoring is the process of monitoring the dark web to identify potential threats. It helps to react to risks before they cause damage.
In addition to private individuals, it is also important for companies that manage sensitive data and need to protect themselves and their customers from the dangers of the dark web.
How does Dark Web Monitoring work?
In principle, every user can make their own way onto the dark web. However, you first need special software such as the TOR browser. In addition, there is no Google for the dark web where you can simply search for the information you need. Accordingly, you need the exact dark web addresses. There are also dangers and viruses lurking everywhere.
Authorities therefore recommend that you do not go looking for them yourself. It is comparable to a private individual who, without the appropriate training and protective equipment, tries to single-handedly convict a drug cartel. It might work in movies, but in real life it’s usually not a good idea.
This is why there are special tools that have been developed specifically for dark web monitoring.
These security software tools use advanced technologies such as algorithms and AI to constantly scan the dark web and identify potential risks. These tools are able to efficiently analyze encrypted areas and extract relevant information.
Our recommendation: HackCheck
In recent years, one tool has become particularly popular with many users: HackCheck! The security tool was specially developed to inform users whether their personal data has appeared on the dark web. This tool provides an additional layer of security and complements Dark Web Monitoring. It enables users to react quickly to potential threats and improve their digital security.
If HackCheck detects that the user’s data is in circulation during dark web monitoring, the user immediately receives an alert. In addition, information is provided on which hack it is, where the data comes from and what to do next to prevent damage.
Concluding words
Sources:
Statistics on current losses due to cybercrime: https://www.einnews.com/pr_news/606505844/cybercrime-damages-to-cost-the-world-8-trillion-usd-in-2023
FAQ
Fast action is crucial. Change affected passwords and monitor your accounts. In particular, check whether you also use the e-mail address and password in question with other online services and change these access data as well.
Yes, as long as it is used within the framework of the applicable laws and for legitimate purposes.
It can increase security, but there is no guarantee of absolute security on the Internet.
Regular monitoring is recommended, as threats are constantly evolving. Ideally, this monitoring should take place permanently or daily.
Did you find the article helpful? If so, leave us a good review.
Your page rank: